
Google Play has given the boot to 16 apps with more than 20 million combined installations after researchers detected malicious activity that could cause the Android devices they ran on to drain batteries faster and use more data than normal.
The apps provided legitimate functions, including flashlight, camera, QR reading, and measurement conversions, security firm McAfee said on Wednesday. When opened, however, the apps surreptitiously downloaded additional code that caused them to perform ad fraud. From then on, infected devices received messages through the Google-owned Firebase Cloud Messaging platform that instructed them to open specific web pages in the background and select links to artificially inflate the number of clicks ads received.
“Mainly, it is visiting websites which are delivered by FCM message and browsing them successively in the background while mimicking user’s behavior,” McAfee’s SangRyol Ryu wrote. “This may cause heavy network traffic and consume power without user awareness during the time it generates profit for the threat actor behind this malware.”
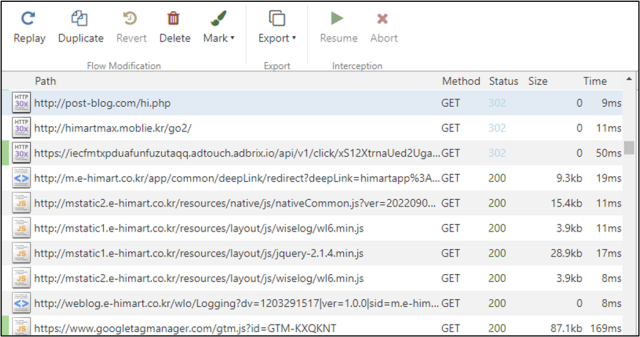
The post included the following screenshot illustrating a small sampling of the additional network demands a device made when performing the fraud.
All of the malicious apps came with a code library named com.liveposting, which acts as an agent and runs hidden adware services. Other apps also came with an additional library called com.click.cas, which focused on the automated clicking functionality. To conceal the fraudulent behavior, the apps waited about an hour after installation before running the libraries.
Ad fraud works through affiliate programs, which allow a third party to receive a cut of the ad revenue in return for providing links that lead end users to ads. Rather than genuinely bringing real users to the site, the fraudsters simulate the referral using bots or other automated methods to mimic real user engagement.
The apps detected by McAfee include:
| Package name | SHA256 | Name | Downloaded |
| com.hantor.CozyCamera | a84d51b9d7ae675c38e260b293498db071b1dfb08400b4f65ae51bcda94b253e | High-Speed Camera | 10,000,000+ |
| com.james.SmartTaskManager | 00c0164d787db2ad6ff4eeebbc0752fcd773e7bf016ea74886da3eeceaefcf76 | Smart Task Manager | 5,000,000+ |
| kr.caramel.flash_plus | b675404c7e835febe7c6c703b238fb23d67e9bd0df1af0d6d2ff5ddf35923fb3 | Flashlight+ | 1,000,000+ |
| com.smh.memocalendar | 65794d45aa5c486029593a2d12580746582b47f0725f2f002f0f9c4fd1faf92c | 달력메모장 | 1,000,000+ |
| com.joysoft.wordBook | 82723816760f762b18179f3c500c70f210bbad712b0a6dfbfba8d0d77753db8d | K-Dictionary | 1,000,000+ |
| com.kmshack.BusanBus | b252f742b8b7ba2fa7a7aa78206271747bcf046817a553e82bd999dc580beabb | BusanBus | 1,000,000+ |
| com.candlencom.candleprotest | a2447364d1338b73a6272ba8028e2524a8f54897ad5495521e4fab9c0fd4df6d | Flashlight+ | 500,000+ |
| com.movinapp.quicknote | a3f484c7aad0c49e50f52d24d3456298e01cd51595c693e0545a7c6c42e460a6 | Quick Note | 500,000+ |
| com.smartwho.SmartCurrencyConverter | a8a744c6aa9443bd5e00f81a504efad3b76841bbb33c40933c2d72423d5da19c | Currency Converter | 500,000+ |
| com.joysoft.barcode | 809752e24aa08f74fce52368c05b082fe2198a291b4c765669b2266105a33c94 | Joycode | 100,000+ |
| com.joysoft.ezdica | 262ad45c077902d603d88d3f6a44fced9905df501e529adc8f57a1358b454040 | EzDica | 100,000+ |
| com.schedulezero.instapp | 1caf0f6ca01dd36ba44c9e53879238cb46ebb525cb91f7e6c34275c4490b86d7 | Instagram Profile Downloader | 100,000+ |
| com.meek.tingboard | 78351c605cfd02e1e5066834755d5a57505ce69ca7d5a1995db5f7d5e47c9da1 | Ez Notes | 100,000+ |
| com.candlencom.flashlite | 4dd39479dd98124fd126d5abac9d0a751bd942b541b4df40cb70088c3f3d49f8 | 손전등 | 1,000+ |
| com.doubleline.calcul | 309db11c2977988a1961f8a8dbfc892cf668d7a4c2b52d45d77862adbb1fd3eb | 계산기 | 100+ |
| com.dev.imagevault | bf1d8ce2deda2e598ee808ded71c3b804704ab6262ab8e2f2e20e6c89c1b3143 | Flashlight+ | 100+ |
In a statement, a Google spokesperson noted that all apps reported by McAfee had been removed. The representative went on to say: “Users are also protected by Google Play Protect, which blocks these apps on Android devices.” The spokesperson didn’t answer a follow-up question asking how the apps racked up 20 million installations if they’re blocked.


